


Gartner predicts that by 2025, 51% of enterprise IT spending in critical areas will shift to cloud-based solutions. As businesses move their technology stacks to the cloud, the need for secure cloud environments becomes increasingly important. That is where a Zero Trust Cloud model comes in.
What Is a Zero Trust Cloud?
For beginners, a Zero Trust model of the cloud is one in which no stakeholder is given a free pass for accessing cloud resources, irrespective of the devices, Identities, Location, or applications they use to gain entry. Every user or device must be subject to continuous verification before being permitted to enter the cloud environment for any operations till the end of the session.
In the past, enterprises had their security objectives defined on the strengths of the underlying network and application interfaces. But in a Zero Trust model, the focus shifts to users, resources, and assets on the cloud.
The single biggest philosophy powering a Zero Trust model is the fact that irrespective of the geographic or network location, no user account or their devices are given a trust immunity for accessing cloud resources. This model of security is on a roll as studies estimate that the Zero Trust Security solutions market will reach $51.6 billion by 2026.
Why Is Zero Trust Cloud the Future of Software Products?
In the evolving technology landscape for enterprise software products, Zero Trust cloud makes for the perfect choice as the default cloud security option for deployment. Here are 4 reasons why a Zero Trust Cloud model is the future of software products:
Related Insights: Will Cloud Security Become Easier or Harder for Enterprises?
Perimeter Security Measures are Inadequate
In the past, an organization had extensive control over its digital assets. Most employees worked from an office building with protected and guarded internet connections and secured devices with security control software installed. Fast forward to today, the work landscape has changed. Remote work, BYOD, and other workplace trends have expanded the boundaries of the digital ecosystem within the workplace.
The corporate network or cloud is accessed by a number of users through various devices ranging from company laptops to personal smartwatches to even home internet connections. Every single access request needs to be validated before giving them permission to leverage critical cloud resources. Thus, only a Zero Trust model works in the best interest of the organization in this context.
Crowded SaaS Application Challenges
Most enterprises today rely on several SaaS services to power their digital business. For example, a retailer may use different cloud solutions for their CRM, ERP, eCommerce, HRM, and finance needs. All of these SaaS services may need access to critical data and resources which may be stored in an enterprise cloud storage service. Furthermore, these applications may have to interact with each other, exchange data, and enable transactional processing of data from other systems over the normal course of operations.
Related Insights: How Financial Sector Will Look at Cybersecurity in 2023
From a security perspective, all these activities between SaaS software happen on the cloud and through different API calls or integration interfaces. Every point of contact between the applications is a potential surface that is vulnerable to security threats. Moreover, each application may follow its own defined security standards and frameworks, which can be risky.
Having a Zero Trust Cloud approach brings a consistent sense of security management to this highly interconnected cloud ecosystem. Every application needs to undergo verification and continuous adherence to foundational security compliance outlined by the Zero Trust implementation framework for the organization’s cloud assets.
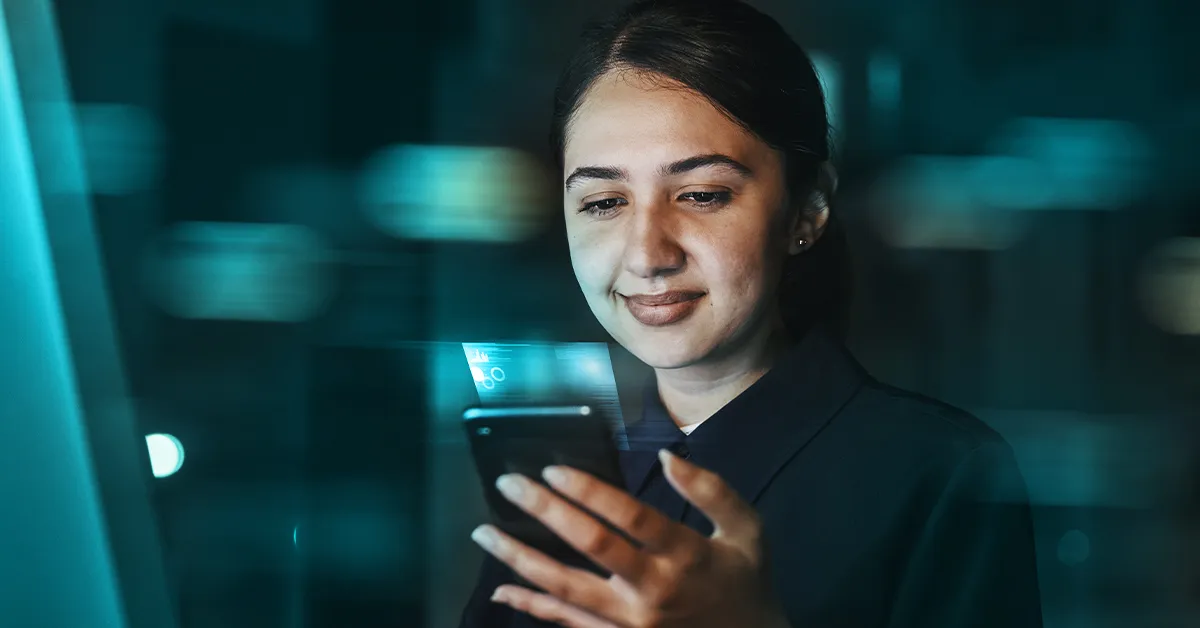
Enforce Identity Management at the Roots
With a Zero Trust approach, enterprises can now enable seamless integration of identity verification measures into every cloud touch point and verify access across the organization’s digital ecosystem. By linking every software used with the identity verification system and following a Zero Trust approach, the IT team can safely empower the use of any modern cloud solutions. They can stop worrying about security risks that often arise due to compromised user identities.
Related Insights: How to Crack the Zero-Trust Approach for Enterprise Security
This helps accelerate digital innovation as new applications can easily be added to the technology stack. Users are empowered to use them without fear seamlessly once they have validated their entry credentials.
Enable Risk Isolation
A key advantage of Zero Trust is that the IT team gets a clear picture of every digital endpoint and knows which user or device has accessed it at what time. This precise insight helps to easily respond to any external threat that manages to move laterally or break into the corporate network through any unconventional method.
Once the attack node is identified, they can easily isolate it by restricting further access to that node and then take steps to rectify and bring up the node to its original state after resolving the threat.
In a Nutshell
With enterprises continuing to grow their cloud workloads, enabling a secure ecosystem to build newer digital capabilities is of critical importance. Having a Zero Trust model of operations will ensure that your cloud investments are protected.
But implementing a Zero Trust model requires a holistic approach that comprises a range of iterative and continuously evolving programs. It is always good to have a trusted partner like Xoriant to assist in building Zero Trust credentials for your cloud initiatives.
Check out our related PDF: OpenStack Private Cloud
Ready to take your cloud to the next level with a Zero Trust model?




 View Previous Blog
View Previous Blog





